The GLBA affects all financial institutions directly. This comprehensive guide provides an in-depth understanding of the GLBA, including all its latest updates and amendments. Let’s dive in. Intro to the GLBA The Gramm-Leach-Bliley Act (GLBA for short) is a US federal law that requires “financial institutions” – defined as companies offering customers financial products or services like loans, financial or … Read More
The Human Factor: The Perfect Employee Training

Part 2 of 3: Reducing Data Leaks + Data Security Awareness Employees are responsible for 90% of all data breaches! That’s why Part 1 of this mini-series discusses the basics of data leaks, while Part 2 tackles the source of the problem: Human error. This is the last employee training you’ll ever need! 1. Intro to Information Security All employees … Read More
Data Loss Prevention: 3 Basic Steps to Data Protection
$4.44 million. That’s the average cost of a data loss instance in 2025. Unless you’ve got that kind of cash just lying around, taking steps toward Data Loss Prevention will be your best option. But who’s keeping your data safe? Intro to Data Loss Prevention Before you get anywhere near avoiding that 4-million-dollar “hit” to the yearly budget, you first … Read More
The Human Factor: How to Eliminate Data Breaches Caused by Employees

Part 1 of 3: Data Leak Basics (Part 2, The Perfect Employee Training; Part 3, 10-Point Data Security Checklist) Nearly 90% of breach incidents are caused by human error. This 3-part mini-series tackles the subject head-on, covering everything from root causes and prevention techniques to the perfect employee training. Let’s get started. What is a Data Leak? A data leak, … Read More
Fast & Accurate Data Breach Resolution
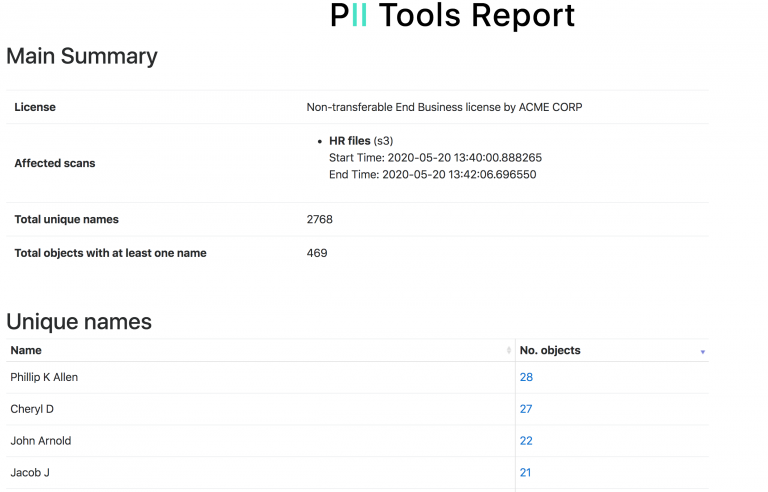
You’ve suffered a data leak, and the clock’s already ticking. Oh, and it’s a large dataset, too. Where do you even start to locate every single instance of PII involved? Let’s get into it! Breach Incident Scanner Discovering leaked sensitive information and PII by hand is completely unrealistic for large datasets, so automated solutions like PII Tools come in handy. … Read More
Can AI Accurately Identify Person Names in Text?

Detecting person names correctly while avoiding false positives is a real time-saver for breach investigations, DSARs, and regulatory compliance. But can this process be automated with AI? Let’s find out. Person Name Identifiers A person name identifier is any information that can be used to directly or indirectly identify an individual, with their actual name being the primary example. Use … Read More
PII and Its Many Forms

Sensitive data and personal information come in many shapes and sizes. And with so many different regulations around the globe, it’s easy to confuse one with another. These are the basics of PII and every form you’ll find it in. Let’s get into it. Understanding PII The world of sensitive data protection has its own terminology you’ll need to be … Read More
How to Avoid Uploading Sensitive PII to Microsoft Copilot

AI tools like ChatGPT and Microsoft Copilot can be useful time savers, but at what cost? There’s no reason you can’t get the best of both worlds—helpful AI models and secure PII. Let’s get into it. Major Copilot Concerns Estimates show that Microsoft Copilot has as many as 33 million active users. And yet, it comes with multiple security risks … Read More
Discovering Person Names in Texts Made Easy
PII Tools streamlines detecting person names with +99% accuracy, even rolling them into Person Cards® for easier export and remediation. Let’s find out how. Basics of Person Name Discovery Detecting people’s names in text is the most fundamental activity in sensitive data discovery. But there are many ways to achieve this task, some more effective than others. The main driver … Read More
How to Scan for PCI DSS Data

Effortlessly locate every piece of credit card data and streamline your PCI DSS compliance with PII Tools. Perform in-house audits, remediate at-risk data, and avoid potential fines. This is how. Intro to PCI DSS The Payment Card Industry Data Security Standard (PCI DSS, for short) is an information security standard organized by major credit card companies (Visa, Mastercard, etc.), aimed … Read More





