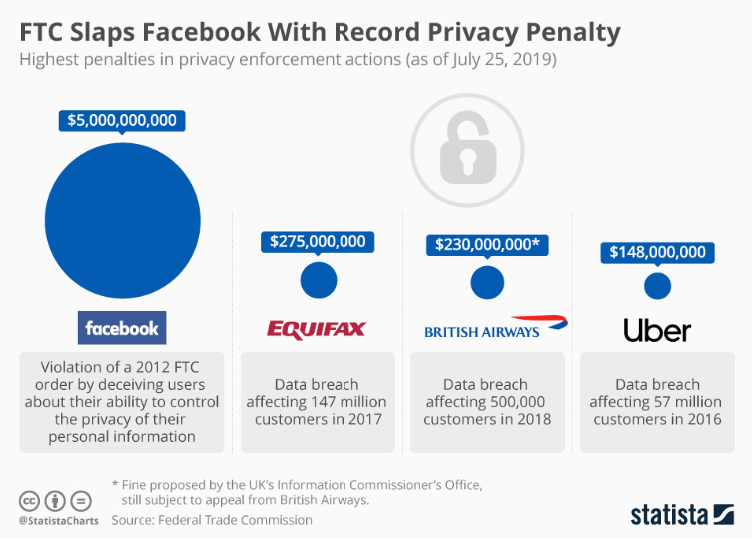
You’ve heard stories of companies running into trouble by not maintaining PII compliance and suffering severe legal ramifications. But what does that mean for you? Out of all the data you have, you’re sure you don’t have any PII lurking around in unwanted or even unlawful areas, right…? Ready or not, your next scheduled PII audit is around the corner. … Read More
What Are Sensitive Data Discovery Tools and How Do They Work?
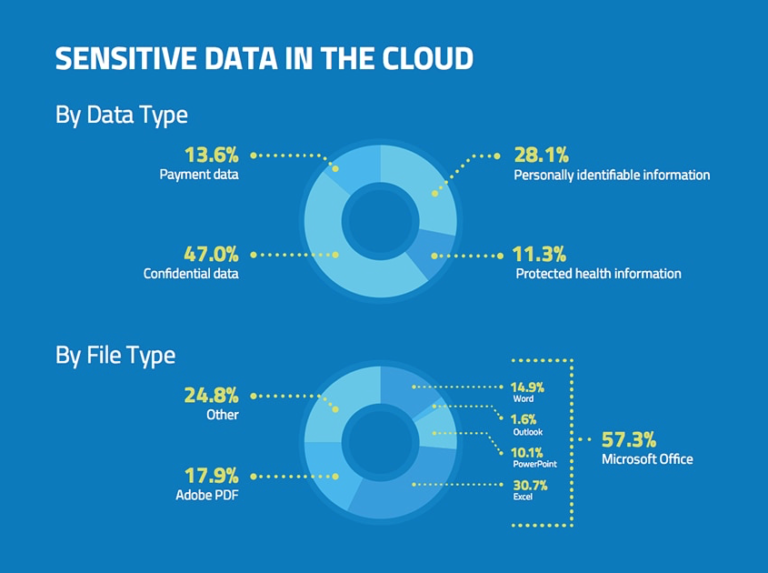
With technology progressing and changing every day, it can sometimes be difficult to keep up with the times. As a business, however, falling behind can mean letting important (and legally binding) information fall through the cracks, disappointing customers and losing the trust of business partners. This is where sensitive data discovery tools come into play. But what exactly are they … Read More
Detect person names in text: Part 2 (Technical)
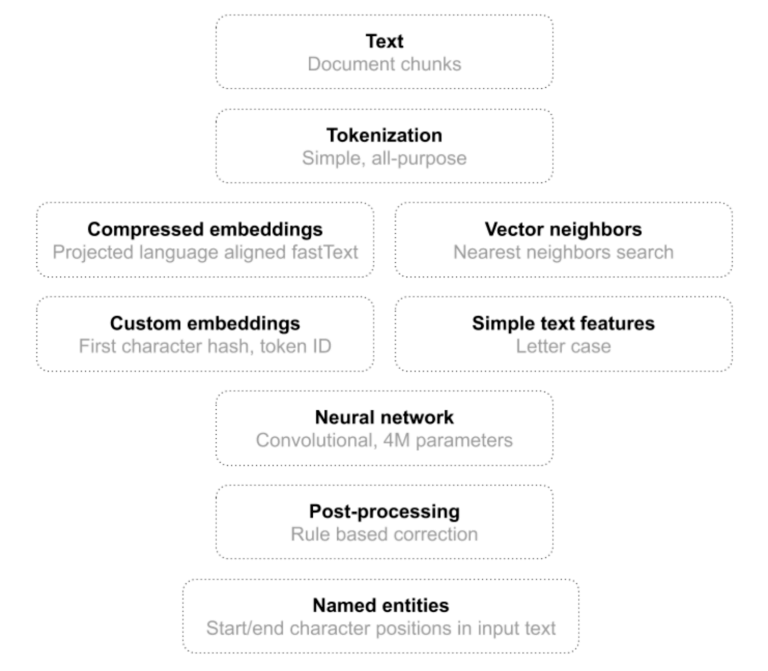
In Detect Person Names in Text: Part 1 (Results), we benchmarked our new named entity recognizer (NER) against popular open source alternatives, such as Stanford NER, Stanza and SpaCy. Today we dig a little deeper into the NER architecture and technical details. First, recall our main NER objectives. In short, we require our NER to be practical, rather than just … Read More
Exclude PII / PCI / PHI From a Breach Report
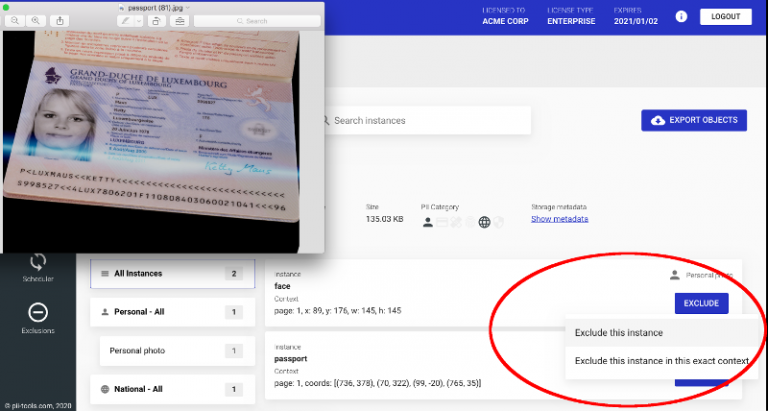
When responding to a breach incident, having a clear idea who’s affected and how is a matter of urgency. Manual discovery of PII information is tedious and costly, so automated solutions come in handy. But how to deal with false positives? PII Exclusions One typical task during a data review is removing unwanted data instances. PII Tools already automates PII … Read More
How To Automate Personal Data Discovery
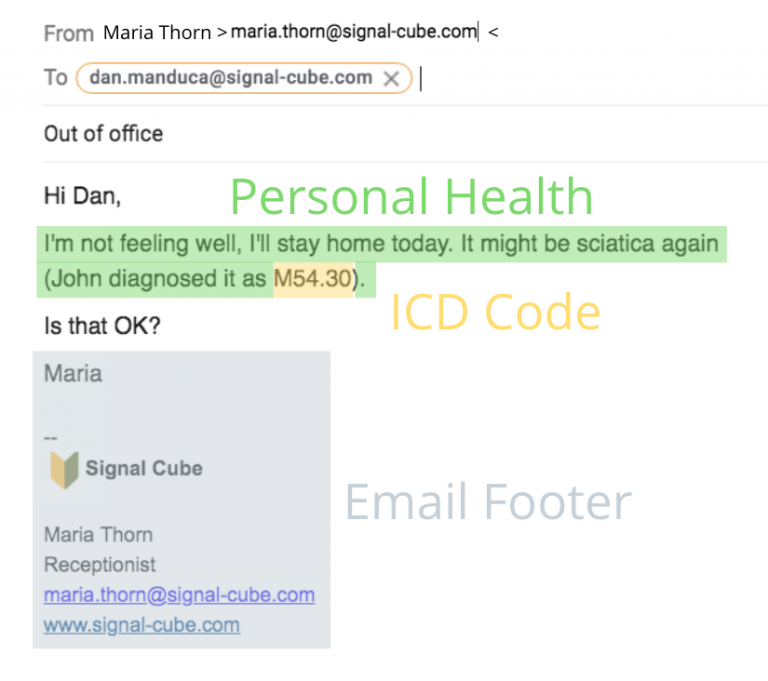
The recent wave of privacy legislations around the world introduced new challenges to experts in litigation support, incident response and auditing. How can modern automation help with reliable PII discovery across emails, files, and databases? 3 Reasons Keywords Fail Traditional approaches based on manually defined keywords and regular expressions fail for three fundamental reasons: High cost. Keywords and regexps are … Read More
NEW PII Drill-Down Reports – Export for Better PII Insights

In the latest February release (version 2.4.0), we combined Personal Data Analytics search with dynamic HTML report generation to make GDPR compliance and auditing easier. PII Tools already supports dynamic PII Analytics queries to locate personal, sensitive, and intimate information. It also generates drill-down PII audit reports for completed data scans. In the latest release, we combined these two capabilities. You can … Read More
Personal Data Analytics
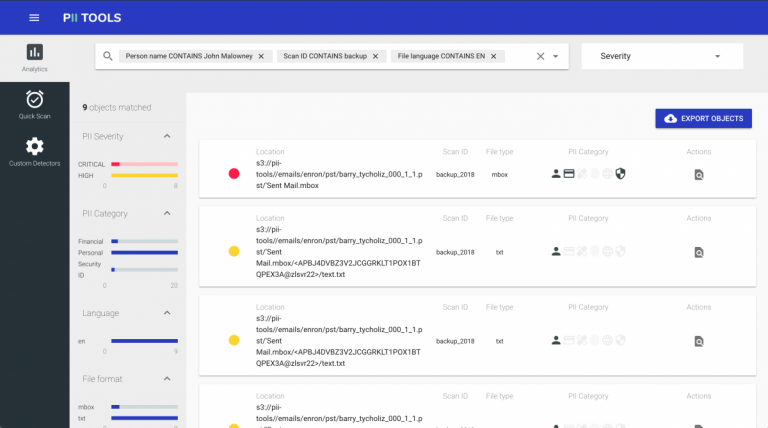
The latest 2.0 release of PII Tools brings a brand new SAR dashboard, allowing targeted personal data search, filtering and analytics. Search for all files on John that contain any financial information, while restricting the results to CRITICAL severity only. Locating Information for Data Subject Access Requests What if you want to find all data related to a specific person … Read More