Around 60% of companies worldwide are hit with ransomware attacks every year! Don’t become another statistic – make your sensitive data and PII completely bulletproof to ransomware and other data leak disasters! The Ransomware Threat Like a form of digital kidnapping, ransomware is any type of malicious software or malware typically designed to block access to a computer system or … Read More
Take Control of Your Personal Data in 2026: A Strategic Guide

In 2026, personal data is no longer just information; it’s the fuel for AI models and the primary target for sophisticated, identity-driven cyberattacks. With the EU AI Act fully active and global privacy fines hitting record highs, simply “having” a privacy policy isn’t enough. You need technical mastery over every byte of sensitive data in your ecosystem. The Problem: “Invisible” … Read More
The Human Factor: How to Eliminate Data Breaches Caused by Employees

Part 1 of 3: Data Leak Basics (Part 2, The Perfect Employee Training; Part 3, 10-Point Data Security Checklist) Nearly 90% of breach incidents are caused by human error. This 3-part mini-series tackles the subject head-on, covering everything from root causes and prevention techniques to the perfect employee training. Let’s get started. What is a Data Leak? A data leak, … Read More
Data Breaches & Consequences

Data breaches are so big these days, they’re measured by records stolen in the millions and even billions! With seemingly so many happening literally every day, let’s explore some of the standout cases and aftermath that followed. Your Data Has Been Leaked The title says it all. At this point, it’s safe to say that various parts of your personal … Read More
Using PII Tools on a Daily Basis
As every GRC team member knows all too well, manually sifting through the company’s seemingly infinite TB of stored data is a full-time job (or a waste of time). But now, with advances in AI-driven data discovery, what does the day of an average PII Tools user actually like? Streamlining Data Discovery The day-to-day mission of any GRC team (Governance, … Read More
Creating Data Leak Reports
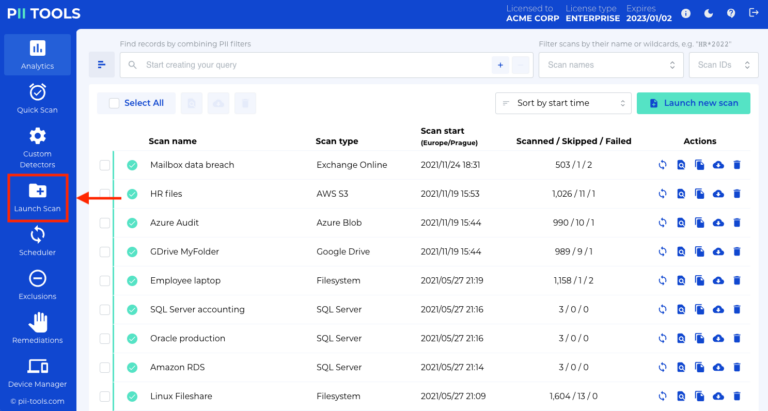
In this guide, you will learn how to create data leak reports with PII Tools. Launching a scan The first step towards the successful management of any data leak is to identify what was in the breached data. Open your PII Tools and, on the left side, select Launch Scan. If you performed the scan already, skip to the next … Read More





