Expanding into the European market is a milestone for any US-based company, but it comes with a significant legal gatekeeper: the General Data Protection Regulation (GDPR). As we move through 2026 and beyond, the cost of “learning as you go” has evaporated.

With the full integration of the EU AI Act, fines for data and AI violations can now reach a staggering €35 million or 7% of global turnover.
For US companies, GDPR compliance is no longer just a legal hurdle. You must actually prove you know where every scrap of European PII (Personally Identifiable Information) lives in your infrastructure, affecting your ability to sell, partner, and operate in the EU.
Does the GDPR Apply to You?
If you collect, process, or store data from people in the EU, the answer is yes. It doesn’t matter where your company is headquartered; what matters is whose data you handle. You are likely in-scope if you:
- Sell to EU customers or track EU website visitors (via cookies/analytics).
- Store EU user data in CRMs, support tools, or AI knowledge bases.
- Process EU employee data or work with EU-based partners.

Recognizing that you have a regulatory obligation is only the first step. To stay compliant, you need to move beyond policies and actually control your data. This checklist outlines the technical and operational pillars required to secure your EU data footprint.
Updated GDPR Compliance Checklist (2026+)
1. Map Your Data (The Discovery Phase)
You cannot protect what you cannot see. US companies often underestimate how far European data spreads across US-based servers and “Dark Data” archives. Achieving total visibility requires a shift from manual sampling to the comprehensive, automated auditing of your entire environment:
- Identify EU Residency: Locate data belonging to anyone protected under the GDPR (anyone currently in the EU, regardless of citizenship).
- Automate Discovery: Use a sensitive data discovery tool to find PII hiding in unindexed PDFs, email archives, and forgotten database columns.
- Know the Flow: Track where data comes from, who accesses it, and which third-party AI systems it’s sent to.
Once you’ve mapped where the data lives, the next priority is determining whether you have the legal right to keep it there.
2. Establish a Legal Basis & Transparency
Under the GDPR, you cannot simply “have” data. You must have a valid legal reason to process it. For US firms, this requires moving away from “implied consent” to documenting a specific justification for every data point collected:
- Explicit Consent: Use clear, affirmative actions (no pre-checked boxes) to ensure users have intentionally opted into data collection.
- Contractual/Legitimate Interest: Ensure these are backed by a proper assessment, and never assume “legitimate interest” is a catch-all that covers every business operation.
- Transparency: Your privacy policy must clearly explain what you collect, how long you keep it, and who you share it with.
Establishing your right to process data is a prerequisite, but for US companies, the challenge often lies in where that processing physically occurs.
3. Solve the Data Transfer Hurdle
Transferring data from the EU to US servers requires specific legal mechanisms to satisfy “Data Sovereignty” requirements. Because US-based cloud storage often triggers strict scrutiny under the GDPR, companies must secure both the legal and physical pathways of their data:
- SCCs & DPAs: Ensure Standard Contractual Clauses and Data Processing Agreements are integrated into every vendor and client contract to provide a legal basis for cross-border transfers.
- Sovereign Auditing: Consider deploying sovereign, on-premise solutions for data scanning. This ensures sensitive EU data doesn’t leave its region during scanning.
Once the jurisdictional boundaries are secured, the focus must shift to the internal technical guardrails that protect the data at a granular level.

4. Implement Technical Guardrails (Privacy by Design)
Security isn’t an afterthought; it’s a requirement. You must minimize the data you collect and store. For 2026 organizations, “Privacy by Design” means moving beyond basic encryption to granular data control at the point of use:
- Data Masking & Redaction: Use masking and redaction to hide PII in testing environments or to remove sensitive fields that aren’t strictly necessary for the task.
- De-Identification: Implement de-identification techniques so that datasets used for AI training or analytics cannot be traced back to an individual.
- Prompt Filtering: Ensure that any data being fed into LLMs or RAG systems is sanitized in real-time to prevent “data sponge” leaks.
While technical guardrails secure the data itself, you must also provide a mechanism for individuals to exercise their legal rights over that data.
5. Enable Data Subject Rights (DSARs)
EU users have the “Right to be Forgotten” and the right to access their data. If this process is manual and chaotic, you are not compliant. For US businesses with fragmented data ecosystems, fulfilling these requests often becomes an administrative bottleneck that risks regulatory scrutiny:
- Automate DSARs: Use identity-centric mapping (like Person Cards®) to pull a complete report for a user in minutes, rather than weeks. This ensures you can meet the strict GDPR response timelines without diverting your entire engineering team.
- Verify Deletion: It’s not enough to simply “delete” a record. You must be able to prove that the individual’s PII has been scrubbed from all backups, archives, and AI training logs to satisfy the “Right to be Forgotten”.
While enabling user rights is a proactive requirement, you must also have a reactive strategy in place for when things go wrong.

6. Prepare for Breach Notification
The GDPR requires you to act at a rapid pace once a vulnerability is exposed. In a 2026 landscape, simply having a “plan” isn’t enough. What you need is the infrastructure to detect and analyze data exposure in real-time:
- Detect & Assess: Have the visibility to identify exactly which PII was involved in a breach immediately. Without automated tools, assessing the impact on EU citizens can take weeks.
- The 72-Hour Rule: You are legally required to notify authorities within 72 hours of discovering a breach. This window is difficult to meet if you are still manually auditing servers to determine what was lost.
Your technical defenses are only as strong as the people operating them. To move from “compliant on paper” to “compliant in practice,” you must address the final link in the chain: the human factor.
Where US Companies Usually Fail
Identifying your obligations is easy. Maintaining them across a growing infrastructure is where most US firms stumble. These common blind spots represent the highest risk for non-compliance:
- The “One-Time Task” Trap: Treating compliance as a project with an end date is a recipe for failure. In reality, it’s a continuous operational state. Without automated, scheduled discovery, your visibility begins to degrade the moment your last manual audit ends.
- Shadow AI: This is a massive, unmanaged risk. Employees uploading raw customer data into third-party AI tools or LLMs creates invisible data flows that bypass your security perimeter and violate residency requirements (AI Data Protector).
- Ownership Gaps: When data is scattered across departments, accountability often vanishes. Without a single source of truth, it becomes impossible to fulfill deletion requests or prove data minimization to a regulator.
Manual compliance cannot keep pace with modern data velocity. To maintain a defensible position, these requirements must be integrated into your infrastructure as a background process.
Turn Compliance into a System with PII Tools
Compliance shouldn’t be a friction point that slows your expansion. By replacing manual oversight with an automated framework, PII Tools transforms GDPR requirements from a legal headache into a scalable technical asset.
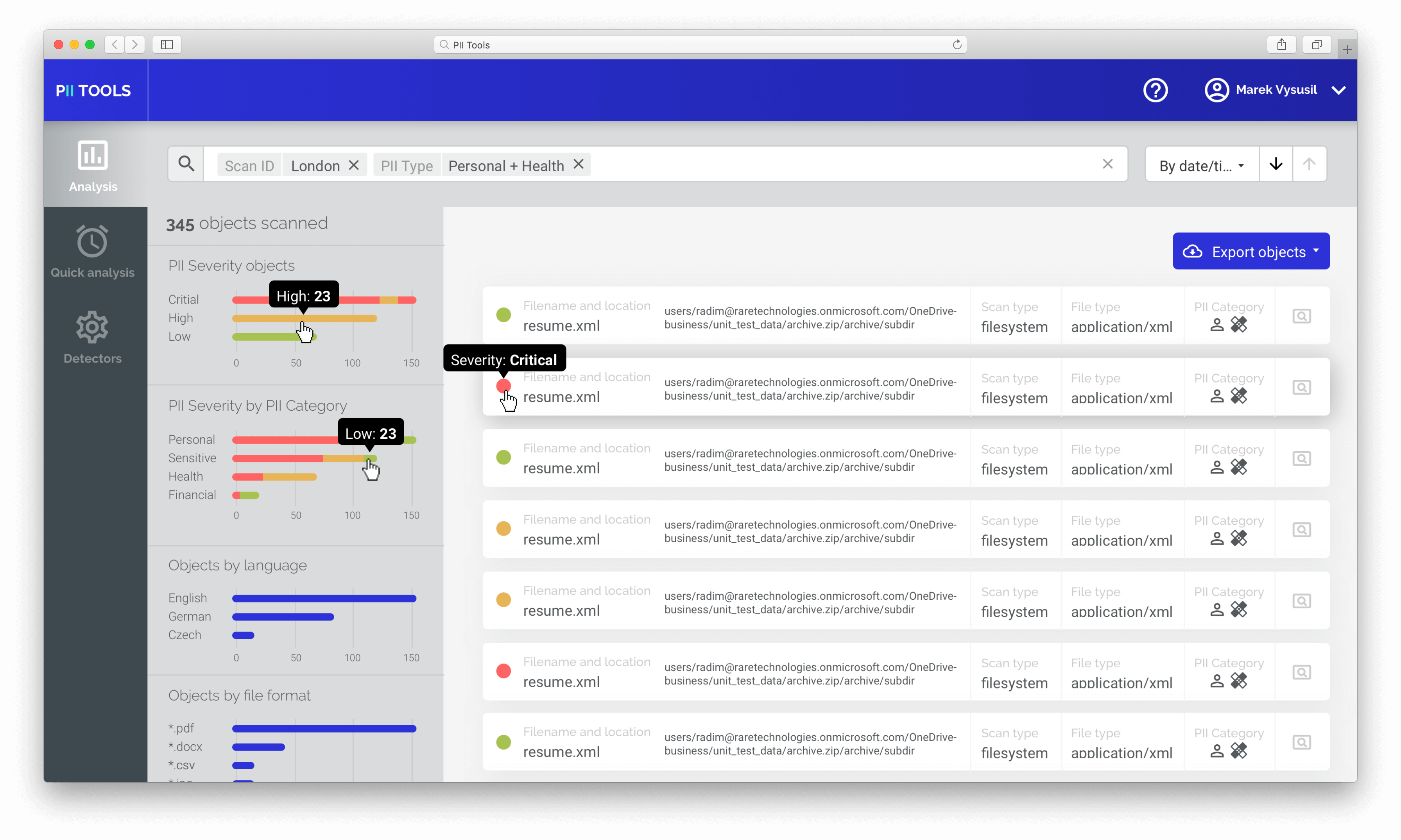
Our platform handles the heavy lifting by automatically discovering sensitive data, including “Dark Data” hidden in archives, and de-risking your AI pipelines through high-fidelity masking and anonymization. This move away from point-in-time audits creates a state of permanent audit-readiness, always prepared for regulatory scrutiny.
Don’t Let Regulatory Complexity Become the Bottleneck to Your International Growth. Build a Defensible, Automated Infrastructure that Protects Your Data and Your Reputation.





