The landscape of data privacy has shifted. In 2026 and beyond, simply finding strings of text isn’t enough to satisfy auditors or modern regulations like the EU AI Act. Whether you’re preparing for a compliance audit or starting a trial, knowing how to evaluate sensitive data discovery software is vital. To avoid wasting time on “legacy” tools that rely on … Read More
How to remediate PII?
Within the world of sensitive data discovery, there are many roads you can take to remain compliant to mandatory regulations. Unfortunately, many of these roads can leave you with more questions than answers. If you’re looking for a simpler route to protect your company’s data, SaaS is right for you. What is SaaS? Pronounced /sæs/, SaaS stands for Software as … Read More
Scanning Office 365 for sensitive PII information

Discover personal & sensitive data inside Office 365 accounts and remediate it. This includes both structured and unstructured data in Microsoft OneDrive, Microsoft Exchange Online, and Sharepoint Online. What does “support Office 365” mean? With PII Tools, you directly find, review, and remediate personal and sensitive information in documents, emails, and tables shared within your company’s Office 365 accounts. No … Read More
Exclude PII / PCI / PHI From a Breach Report
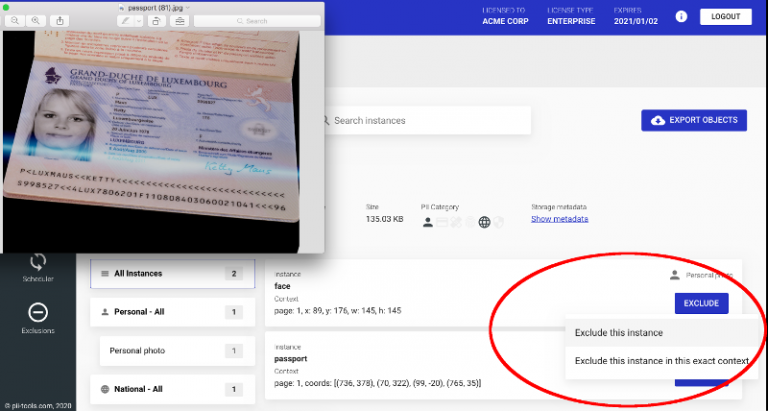
When responding to a breach incident, having a clear idea who’s affected and how is a matter of urgency. Manual discovery of PII information is tedious and costly, so automated solutions come in handy. But how to deal with false positives? PII Exclusions One typical task during a data review is removing unwanted data instances. PII Tools already automates PII … Read More
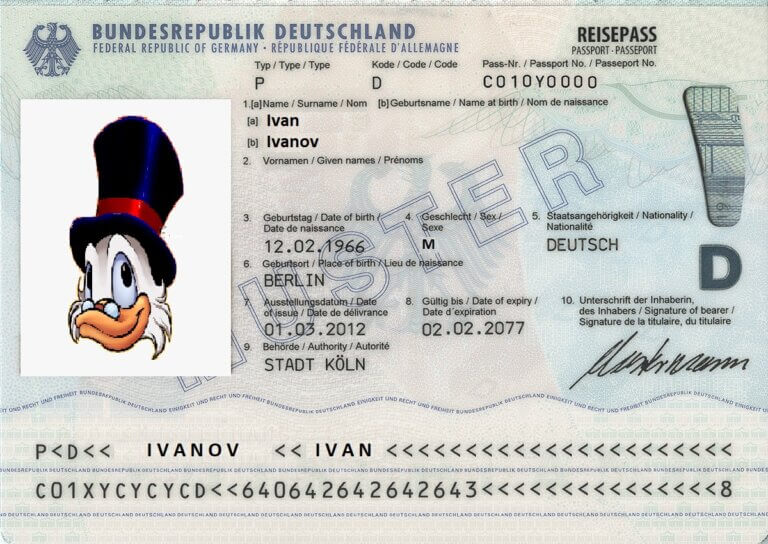
How To Automate Personal Data Discovery
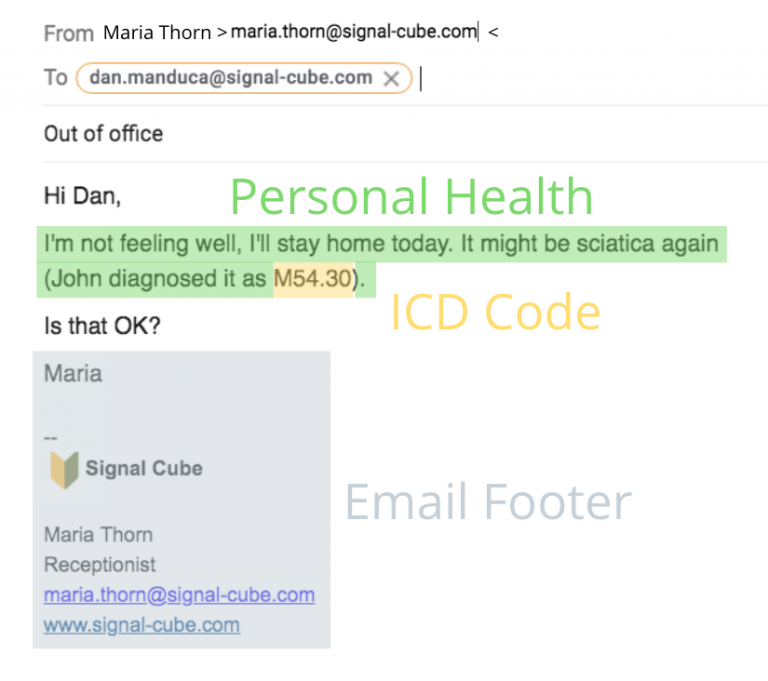
The recent wave of privacy legislations around the world introduced new challenges to experts in litigation support, incident response and auditing. How can modern automation help with reliable PII discovery across emails, files, and databases? 3 Reasons Keywords Fail Traditional approaches based on manually defined keywords and regular expressions fail for three fundamental reasons: High cost. Keywords and regexps are … Read More
NEW PII Drill-Down Reports – Export for Better PII Insights

In the latest February release (version 2.4.0), we combined Personal Data Analytics search with dynamic HTML report generation to make GDPR compliance and auditing easier. PII Tools already supports dynamic PII Analytics queries to locate personal, sensitive, and intimate information. It also generates drill-down PII audit reports for completed data scans. In the latest release, we combined these two capabilities. You can … Read More
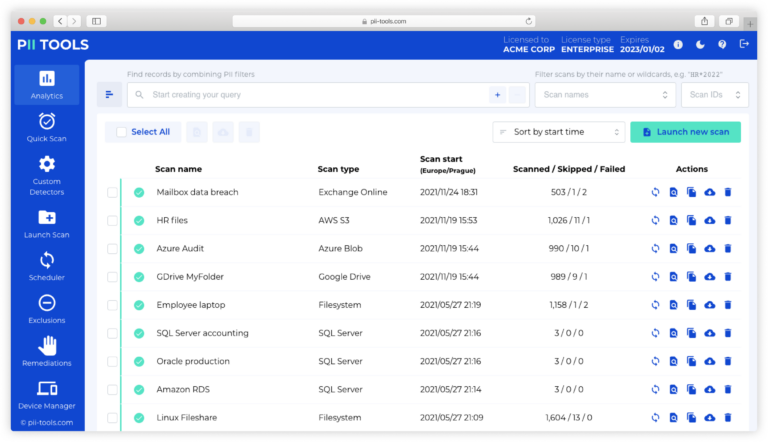
Personal Data Analytics
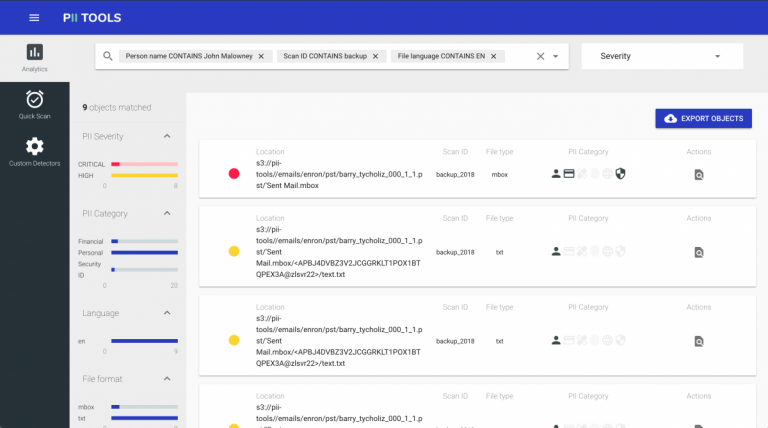
The latest 2.0 release of PII Tools brings a brand new SAR dashboard, allowing targeted personal data search, filtering and analytics. Search for all files on John that contain any financial information, while restricting the results to CRITICAL severity only. Locating Information for Data Subject Access Requests What if you want to find all data related to a specific person … Read More