AI, Regulation, and the Rise of “Technical Truth”
In 2026, data privacy is no longer a legal formality or a checkbox exercise; it’s a core component of business survival.
Regulators have shifted their focus from “policies on paper” to “technical truth,” actively testing whether organizations can actually enforce the rights they claim to protect.
The 2026 Regulatory Landscape: Beyond the GDPR
While the GDPR remains the foundation, 2026 is defined by the convergence of AI governance and a multi-polar regulatory environment.
- The EU AI Act comes into effect on August 2, 2026, forcing organizations to audit their training datasets for bias, provenance, and lawfulness before they ever touch an LLM.
- Regulators are now auditing the actual code behind consent banners. If your “Reject All” button doesn’t technically stop trackers in real-time, you are at risk of million-dollar fines for deceptive design.
- With over 20 US states now enforcing individual privacy laws, manual compliance is mathematically impossible. Automated sensitive data discovery is the only way to manage these overlapping obligations.
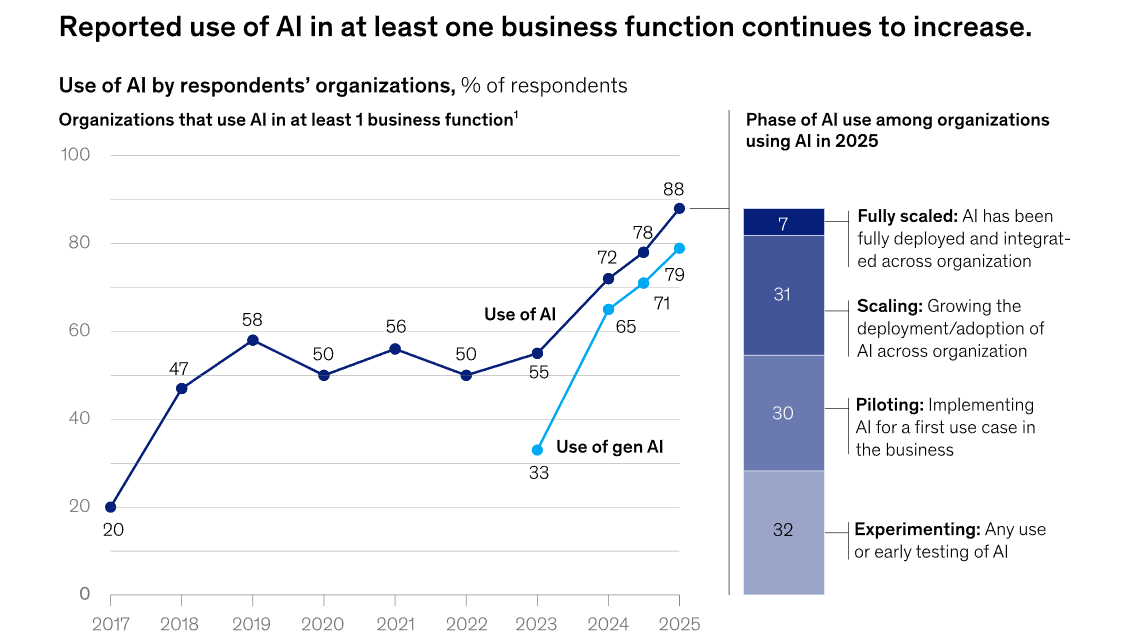
Source: McKinsey & Company
Top 3 Trends Moving Data Privacy Upstream
In 2026, the shift in data privacy is defined by a move toward “Technical Truth”—the ability to prove compliance through real-time data mastery rather than just legal policies. To maintain an edge, organizations are adopting these three transformative trends.
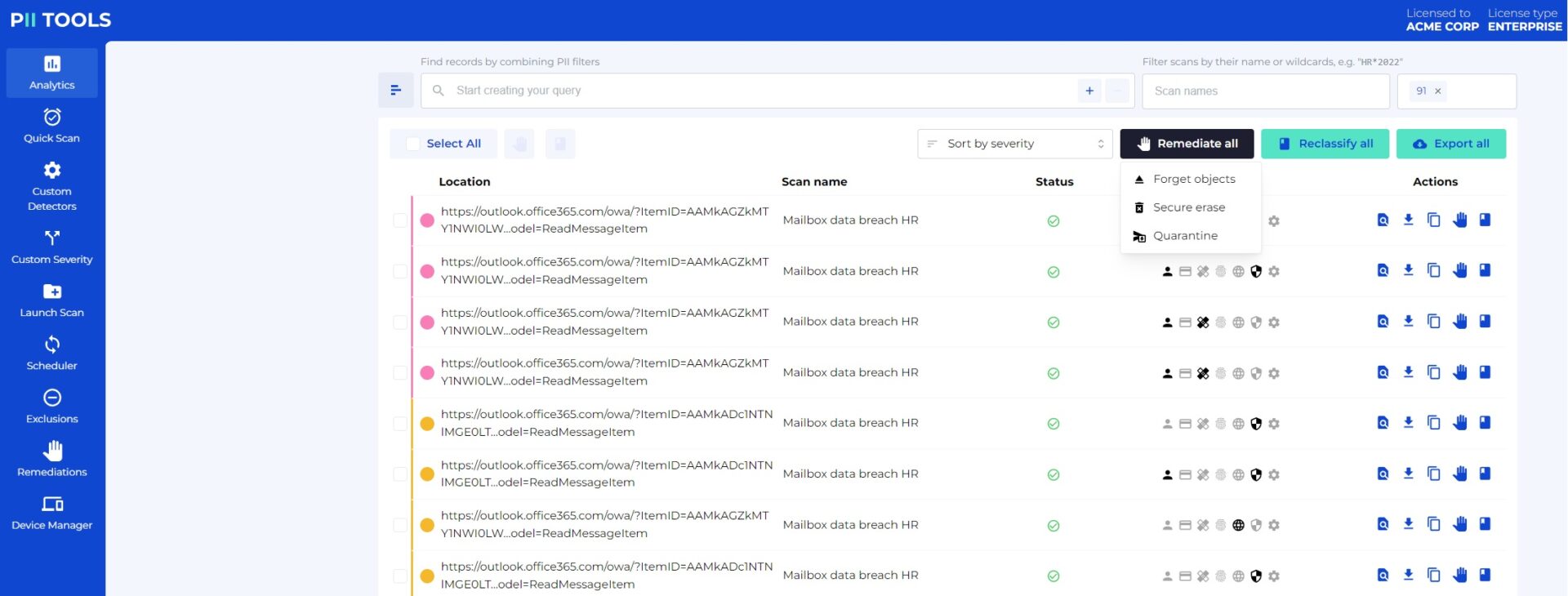
1. From Reactive Blocker to Proactive Posture
Traditional Data Loss Prevention (DLP) often acted as a blunt instrument, blocking productivity to stop leaks. In 2026, the strategy evolved into Data Security Posture Management (DSPM).
Instead of simply reacting to data in motion, a modern AI data scanner provides continuous visibility into data at rest. By analyzing behavioral patterns and data lineage, it identifies and remediates vulnerabilities before they can be weaponized by threat actors.
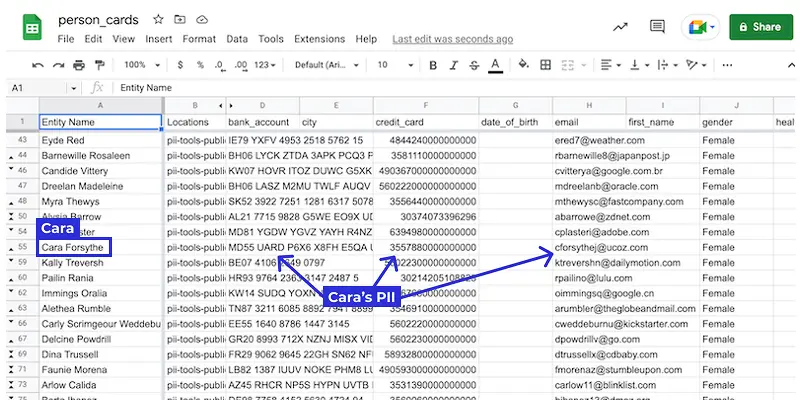
2. The Identity-Centric Compliance Revolution
Regulators no longer focus solely on what data was leaked; they now demand to know exactly whose data was compromised.
This shift has made “hit-based” reporting obsolete. Using proprietary Person Cards®, PII Tools now automatically unifies scattered data points into a single, audit-ready identity. This identity-centric approach transforms a weeks-long administrative nightmare into a process where Data Subject Access Requests (DSARs) can be fulfilled in minutes.
3. AI: The Double-Edged Sword of Defense
While AI creates new risks, such as prompt injections and “agentic” AI attacks, it’s also become the primary tool for defense. In 2026, manual classification is impossible against the scale of modern data sprawl.
By deploying defensive AI, organizations can classify 100,000 documents per hour, allowing security teams to operate at the same speed and sophistication as the automated threats they face.
The 2026 Strategy: From Checkboxes to Technical Truth
Compliance in 2026 is no longer about static documentation; it’s about proving your “technical truth” through the automated mastery of your data environment. Use this roadmap to ensure your infrastructure meets the latest regulatory expectations.
Secure Your AI Supply Chain
Before any dataset touches an LLM or an automated agent, it must be sanitized. Use an AI Data Protector to proactively scan training sets for protected PII. This prevents sensitive information from being “memorized” by models, neutralizing the risk of accidental data leaks through AI prompts.
Step 1) Respect the “Digital Handshake”
User trust is now a technical requirement. Ensure your web infrastructure automatically honors Global Privacy Control (GPC) signals. In 2026, regulators treat a browser’s GPC signal as a legally binding “Do Not Sell” request, and ignoring this signal is a fast track to deceptive-design penalties.
Step 2) Illuminate Your “Dark Data”
High-risk data rarely sits in plain sight—it hides in the shadows of your infrastructure. Commit to Transparent Archiving by regularly scanning ZIP, RAR, and PST backups.
Since nearly 80% of an organization’s sensitive data typically resides in these forgotten containers, surface-level scanning is no longer a valid defense during an audit.
Step 3) Master Identity-Level Mapping
The era of “hit-based” reporting is over. To survive intensified transparency audits, you must transition to identity-based reporting.
By utilizing Person Cards®, you can unify scattered fragments of sensitive data into a single, audit-ready view of each individual. This is the only way to manage modern transparency requirements at scale.
Prepare for the “Digital Omnibus”
The EU is currently reviewing the Digital Omnibus Regulation, which aims to harmonize GDPR, the AI Act, and the Data Act into a single entry point for compliance.
The message is clear: the era of fragmented privacy is ending.
Don’t Wait for an Audit. Prove Your “Technical Truth” Today!
Schedule a Live Demo or explore our Virtual Product Tour to see our AI data scanner in action.




