For years, HIPAA compliance was straightforward: protect the Electronic Health Record (EHR) system, and you protect the organization. In 2026 and beyond, that approach no longer works. The real risk has shifted to the messy, unstructured “Dark Data” surrounding the EHR. Protected Health Information (PHI) now leaks into email attachments, billing exports, shared drives, and increasingly, AI workflows. In the … Read More
Global University Data Breach: 230+ Million People Affected

On May 7, 2026, students from over 9000 universities around the world received the terrifying news: Your sensitive information is included in a large-scale data breach, and the ransom is due in just 5 days! Massive Ransomware Strike This is the frightening reality for more than 231 million people right now. MIT, The University of Toronto, Penn State University, and … Read More
Use AI Without Violating Data Privacy Laws (2026 Guide)

2026 was supposed to be the “Year of the AI Agent,” where Large Language Models (LLMs) handle everything from corporate research to automated customer support. However, for many organizations, that promise has been stalled by a sobering technical truth: AI bots are data sponges. Whether your team is summarizing documents in ChatGPT, analyzing datasets in Copilot, or fine-tuning a proprietary … Read More
The Human Factor: How to Eliminate Data Breaches Caused by Employees

Part 1 of 3: Data Leak Basics (Part 2, The Perfect Employee Training; Part 3, 10-Point Data Security Checklist) Nearly 90% of breach incidents are caused by human error. This 3-part mini-series tackles the subject head-on, covering everything from root causes and prevention techniques to the perfect employee training. Let’s get started. What is a Data Leak? A data leak, … Read More
Can AI Accurately Identify Person Names in Text?

Detecting person names correctly while avoiding false positives is a real time-saver for breach investigations, DSARs, and regulatory compliance. But can this process be automated with AI? Let’s find out. Person Name Identifiers A person name identifier is any information that can be used to directly or indirectly identify an individual, with their actual name being the primary example. Use … Read More
PII Examples

Below you’ll find an example list of Personally Identifiable Information, or PII, to help you better understand how it can appear in the real world. You’ll also find FREE downloadable files attached to each point with specified (fake) PII examples you can then use to test your discovery solution. Enjoy. PII includes, but is not limited to: Names: Full name, … Read More
Employee Training: PII Security and Data Management

The vast majority of mistakes that lead to breached data are accidental and caused by human error. What are the best ways to train employees to handle PII and build unshakable security awareness? Accidental Data Leaks Humans are imperfect. Even if you have 20+ years of experience in data security and breach prevention, you can still slip up and make … Read More
Regular Audits: Do You Really Need Them?

There’s nothing worse than wasting time and money, so is there any benefit to reviewing the data you store? Well, unless you want to be like the kid who never studies for tests, regular audits may be the only thing keeping you out of the principal’s office. To Audit or Not to Audit? By this point, I would hope none … Read More
Do They Even Matter?—The 3 Largest GDPR Fines To Date

For years now, the GDPR has been criticized for offering more bark than bite. As the fines stand, many mega-companies like Amazon and Google are simply getting away without a scratch. All this has left us wondering, what are the 3 biggest GDPR fines so far, and do any of them actually matter? Knowing the GDPR Before we get to … Read More
Creating Data Leak Reports
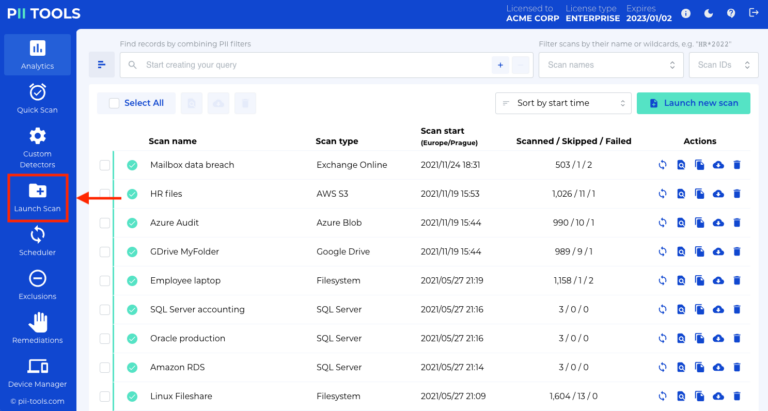
In this guide, you will learn how to create data leak reports with PII Tools. Launching a scan The first step towards the successful management of any data leak is to identify what was in the breached data. Open your PII Tools and, on the left side, select Launch Scan. If you performed the scan already, skip to the next … Read More
- Page 1 of 2
- 1
- 2





