Personal data comes in many shapes and sizes. As business owners, company employees, and internet consumers, it’s our job to know what personal data is and how to locate and protect it. But now that the new millennium is well on its way, is there any new technology out there that can help? Where to Get Started? Step one is … Read More
Learning the Difference Between Data Privacy and Data Security
Companies often believe that by securing their sensitive data, they automatically comply with the requirements of various data privacy regulations (GDPR, HIPAA, CCPA, etc.). Unfortunately, this is not the case. Let’s take a look at these two terms to understand the difference and make sure you adhere to both. It’s a bad habit to treat data security and data privacy … Read More
What Are Sensitive Data Discovery Tools and How Do They Work?
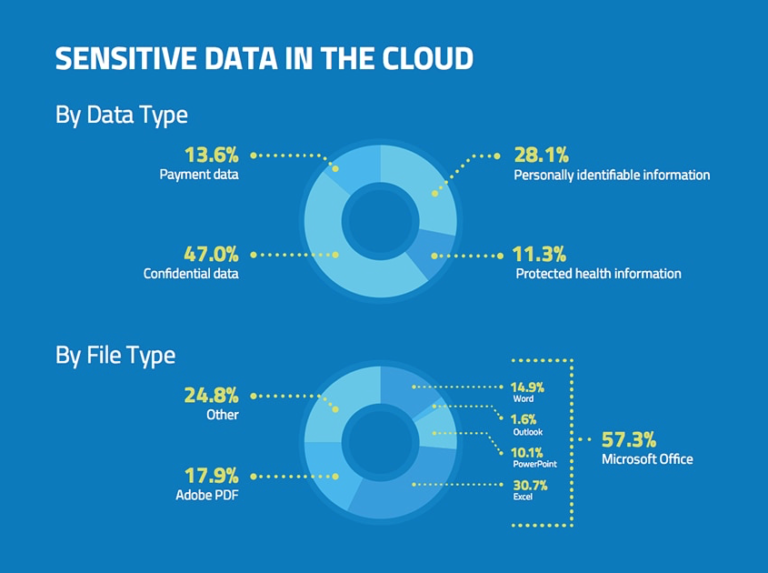
With technology progressing and changing every day, it can sometimes be difficult to keep up with the times. As a business, however, falling behind can mean letting important (and legally binding) information fall through the cracks, disappointing customers and losing the trust of business partners. This is where sensitive data discovery tools come into play. But what exactly are they … Read More
Detect person names in text: Part 2 (Technical)
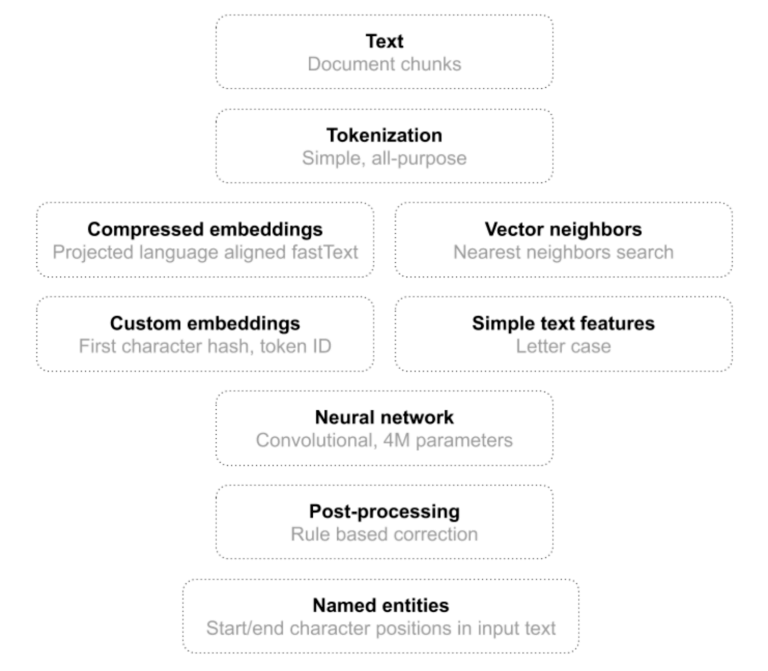
In Detect Person Names in Text: Part 1 (Results), we benchmarked our new named entity recognizer (NER) against popular open source alternatives, such as Stanford NER, Stanza and SpaCy. Today we dig a little deeper into the NER architecture and technical details. First, recall our main NER objectives. In short, we require our NER to be practical, rather than just … Read More
Exclude PII / PCI / PHI From a Breach Report
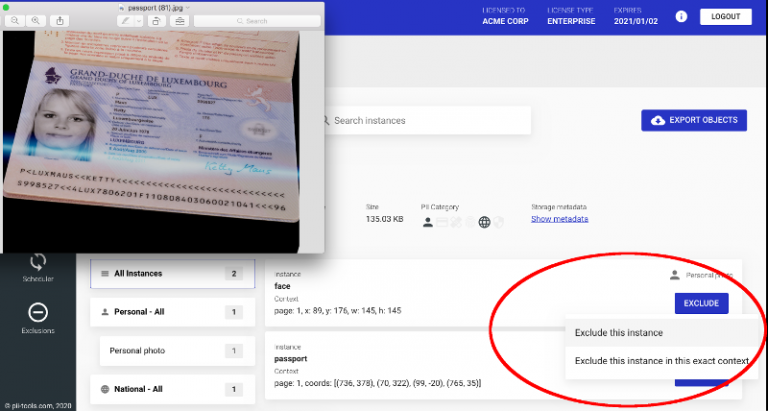
When responding to a breach incident, having a clear idea who’s affected and how is a matter of urgency. Manual discovery of PII information is tedious and costly, so automated solutions come in handy. But how to deal with false positives? PII Exclusions One typical task during a data review is removing unwanted data instances. PII Tools already automates PII … Read More





